
Malaysia’s new digital transformation era demands stronger cyber security measures says Fortinet
The gradual migration of critical business operations to the cloud, on-demand computing and the proliferation of the Internet of Things in both offices and homes has resulted in a new era of digital transformation not just for Malaysia but the world as well. With these new ways of doing business also come new opportunities and with them new threat vectors that include a plethora of cyber-attacks and worse which can bring about financial ruin in a heartbeat.
Anthony Lim, Principal Consultant for Fortinet SEA and HK sharing more about the threat landscape for cyber security in Malaysia
According to marketing research firm Cybersecurity Ventures, cybercrime damages are predicted to cost the world US$6 trillion annually up to 2021, up from US$3 trillion in 2015 with cybercrime damage amounting to loss of data, productivity,financial data theft and sundry other threats to organisational assets and reputation.
Companies are increasingly embracing these new technologies and systems for the better, many local companies unfortunately deploy ad-hoc one-off security solutions rather than a comprehensive, multi-vector solution that can address the myriad of potential cyber attack threats to an organisation. While these piecemeal solutions can tackle the odd low-level exploit or two, it’s simply a minor speed bump for more sophisticated attackers who can exploit these chinks in an organisation’s cybersecurity programme.
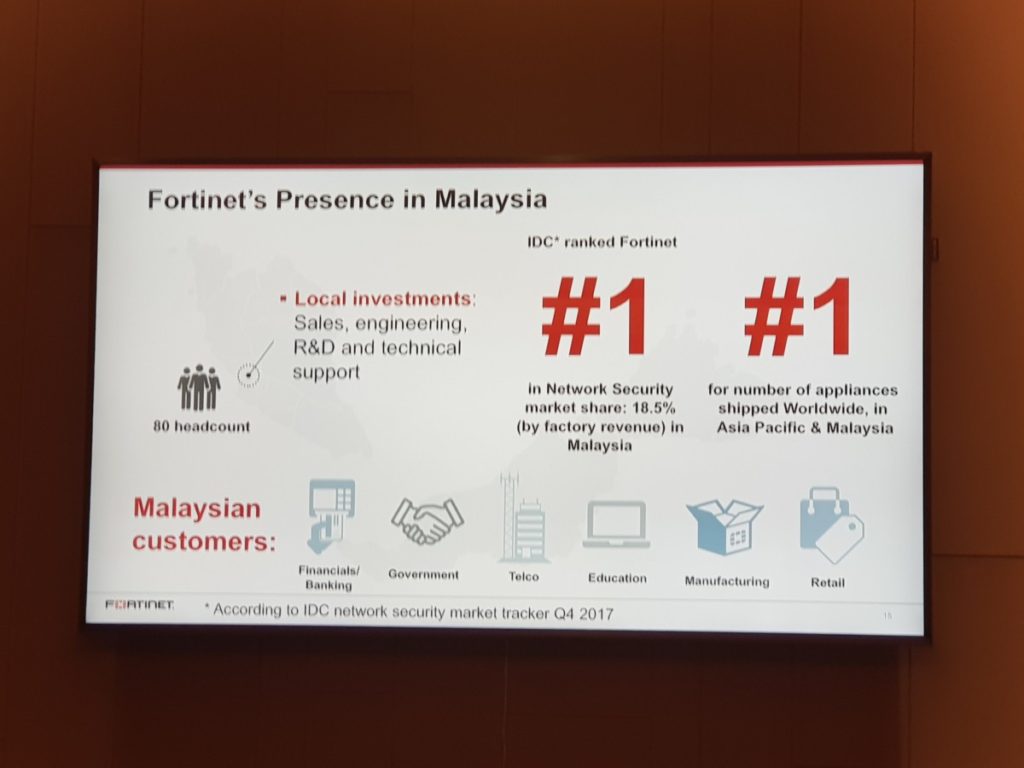 “Organisations in Malaysia must take tough measures to develop a robust cybersecurity strategy and ensure they are primed and ready to stop potential cyber-attacks. In today’s environment of highly sophisticated threats, it is crucial that firms strengthen defences against cybercrime and remain a secure place to do business,” said Alex Loh, Country Manager for Fortinet Malaysia in a recent media briefing where he shared highlights on Fortinet’s operations in Malaysia as well as their performance in the region.
“Organisations in Malaysia must take tough measures to develop a robust cybersecurity strategy and ensure they are primed and ready to stop potential cyber-attacks. In today’s environment of highly sophisticated threats, it is crucial that firms strengthen defences against cybercrime and remain a secure place to do business,” said Alex Loh, Country Manager for Fortinet Malaysia in a recent media briefing where he shared highlights on Fortinet’s operations in Malaysia as well as their performance in the region.

Alex Loh, Country Manager for Fortinet Malaysia
During the briefing, Fortinet espoused for businesses in Malaysia to adopt a more proactive, robust perspective in terms of cybersecurity in terms of not only implementing more comprehensive solutions that cover all avenues but also rigorous employee education as well. They’ve summed up their insight for organisations looking to beef up their cybersecurity protocols into six gems of wisdom:
1. Develop and maintain a holistic security plan with unified policies and protocols.
2. Build security plans around open standards to ensure cohesiveness even when plans and solutions evolve. Any solutions being considered that strays from the larger security picture needs to be reconsidered.
3. Establish single-pane-of-glass visibility for centralized management and orchestration. This must include an active inventory of all devices on the network and an assessment of their state of vulnerability tied to indicators or compromise; as well as an active plan to patch, protect, or replace at-risk devices. Centralised coordination also allows security systems to expand and adapt dynamically as network systems and resources shift and evolve.
4. Share and correlate threat intelligence, both local and global, so that every device is tuned to the latest threats including SIEMs and sandboxing to detect complex or day zero threats.
5. Utilise open standards-based security framework to enable active coordination between devices to respond to a threat, regardless of where it occurs across the distributed and elastic network.
6. Apply automation and artificial intelligence. The time between breach and compromise is dropping by the day and will soon be measured in microseconds. There is no longer the luxury nor resources to hand correlate data and then manually responding to a threat.
